Application Security
Application security is the process of making apps more secure by finding, fixing, and enhancing the security of apps.

Introduction:
The talent of shielding networks, devices, and statistics from unofficial access or unlawful use is known as cyber security. It's also a way to ensure information's confidentiality, integrity, and availability. Program Security is an essential part of Cyber security since it protects data within the application and prevents unauthorized users from accessing it.
Application security focuses on identifying application functionality and use methods, data flow in the application, business logic, access restrictions, and authorization problems in order to safeguard applications and protocols. Following the Secure Application Development Guidelines established throughout the development phase of the application is an important part of application security. For example, to guarantee that bespoke business applications are not exposed to malware, developers must adopt safe application development methodologies.
What is application security?
Application compliance is the practice of generating, mixing or integrating and assessing security protocols into applications to safeguard them from threats like illegal access and alteration.
Why application security is important?
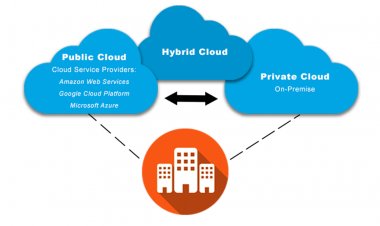
Since now a day applications are usually reachable over numerous networks and linked to the cloud, they are much additional susceptible to security threats and compromises. Finding and repairing vulnerabilities helps to minimize an organization's overall attack surface by lowering security risks.
Vulnerabilities in software are frequent. Even noncritical vulnerabilities can be aggregated for use in attack chains, even if they aren't all significant. Reducing the number of security flaws and vulnerabilities helps to mitigate the total effect of assaults.
It is preferable to take a proactive approach to application security rather than relying on reactive security solutions. Defenders that are proactive are able to detect and neutralize attacks sooner, sometimes before any harm is done.
As companies migrate more of their data, code, and operations to the cloud, the number of assaults on those assets is certain to climb. Such attacks can be mitigated by implementing application security mechanisms.[1]
How does application security work?
Improving security procedures throughout the software development cycle and throughout the application lifetime are examples of security measures. Malicious actors should be prevented from gaining unauthorized access to systems, applications, or data through all app sec operations. Application security's ultimate goal is to prevent attackers from gaining access to, altering, or deleting sensitive or proprietary data.
Any step performed to guarantee application security is referred to as a countermeasure or security control. According to the National Institute of Criteria and Technology, "a protection or countermeasure recommended for an evidence system or an organization to preserve the privacy, reliability, and obtainability of its evidence and to meet a set of established security standards" (NIST).
An application firewall is a type of software countermeasure. Based on the installed application, firewalls determine how files are run and data is managed. The most frequent hardware countermeasure is routers. They prevent an individual computer's Internet Protocol (IP) address from being immediately viewable on the internet.
The following are some more countermeasures:
- Barriers that are standard
- Programmers for encryption and decryption
- Anti-virus software
- Detection and cleanup applications for spyware
- Authentication systems that use biometrics
What are types of application security?
Encryption, Authentication, logging, authorization, and application security testing are all examples of application security structures. Designers may also use code to moderate security defects in apps.
Encryption: For securing your sensitive data from unauthorized persons. The data is encrypted to keep it safe from unauthorized use or criminal use.
Authentication: It mentions the gadgets that software developers technique in a programmer to promise that only lawful operators have access to it. Confirmation checks that the operator is who they say they are. This may be skillful by requesting the user for an operator name and password when logging into an application. Authentication combines aspects like something you know (a password), and approximately you are (your identity) (a thumbprint or facial recognition) something you have (a mobile device).
Logging: If an application's security is breached, logging can help control who increased access to the data and how they did so. The route of which portions of the programmer have been accessed and by who is kept in application log files.
Authorization: After an operator has been verified, he or she may be arranged permission to enter and operate the programmer. The system can ensure that the worker has the authority to admit the programmer by associating the user's identity to a list of approved users. Authentication must occur before authorization in allow for the program to match just validated usernames and passwords to the approved user list.
Application security testing: testing is a vital step in safeguarding that all of these security policies are in place and working effectively.[2]
What are the application security controls?
App security controls are techniques for improving a user's compiled code safety and reducing its exposure to attackers. Many of these options have to do with how programmer re-joins to unusual inputs that a hacker could try to adventure. A programmer can build code for an app that gives them more control over how unforeseen inputs are handled. Fuzzing is a sort of application security testing in which creators examine the outcomes of unpredicted values or inputs to see which ones cause the programmer to behave in an unexpected way, perhaps revealing a safety flaw.
What are the advantages of application security?
- Reduces the danger of both potential threats.
- Promotes the brand's image by showing that having out of the news.
- Consumer data is kept safe, and consumer loyalty is increased.
- Protects sensitive information from being leaked.
- Improves the confidence of key investors and lenders.
- Loshin, P. application security. Available from: https://searchsoftwarequality.techtarget.com/definition/application-security.
- What is Application Security?; Available from: https://www.vmware.com/topics/glossary/content/application-security.html.
 admin
admin