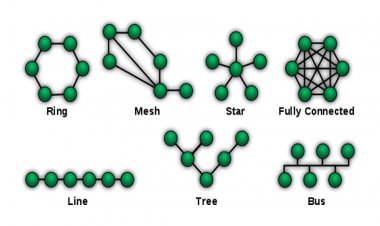
Network Topology
The Network Topology refers to stations connected to a network connection. There...
TOP 5 Installment POS Software in 2026
Managing an electronics or mobile store on installment plans can be tricky without...
Bulk IP changing from DNS after server migration VestaCP
Here I create a Bash script for VestaCP to automatic IP update in all over the domains...
Network Topology
The Network Topology refers to stations connected to a network connection. There...
Internet of Things
Internet of Things (IoT) turns inanimate objects into intelligent ones by linking...
Search Engine Optimization
SEO is the practice of increasing a website's visibility on a search engine's results...
Search Engine Optimization
SEO is the practice of increasing a website's visibility on a search engine's results...
Search Engine Optimization
SEO is the practice of increasing a website's visibility on a search engine's results...
Fifth Generation of Mobile Network
5G is designed to have all the features of 4G with infinite data capacity. The fifth...
Fifth Generation of Mobile Network
5G is designed to have all the features of 4G with infinite data capacity. The fifth...
Internet of Things
Internet of Things (IoT) turns inanimate objects into intelligent ones by linking...
Importance of Painting
painting help safeguard your property and furniture from water and sun damage and...
TOP 5 Installment POS Software in 2026
Managing an electronics or mobile store on installment plans can be tricky without the right tools. The best POS software in 2026...
Top 5 Mobile Shop POS Software in 2026
This Blog reviews top 5 mobile shop POS software systems, comparing features like inventory management, automated billing, customer...
Information Security
Information security helps to keep the data safe from unauthorized access.
Application Security
Application security is the process of making apps more secure by finding, fixing, and enhancing the security of apps.
Network Infrastructure Security
Network Infrastructure Security means protecting your network from unauthorized access.